盗链环境模拟
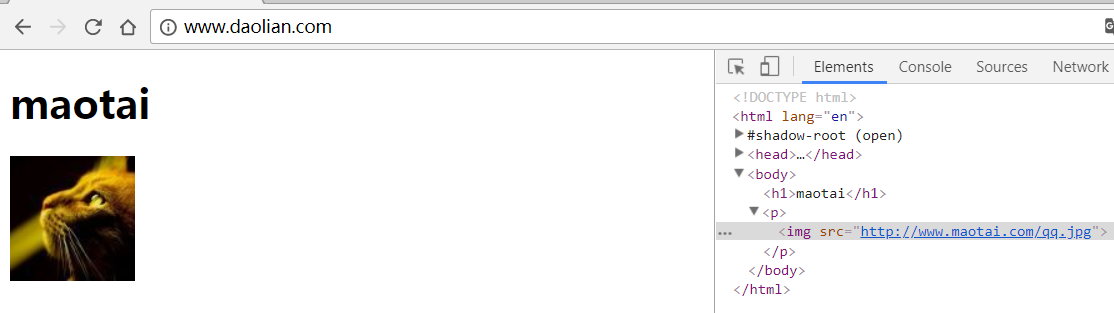
这个页面盗用.
毛台 maotai
搭建2个虚拟主机:
http://www.maotai.com/qq.jpghttp://www.daolian.com/index.html, 这个盗用上面那个站点的图.
worker_processes 1;events { worker_connections 1024;}http { include mime.types; default_type application/octet-stream; sendfile on; keepalive_timeout 65; server { listen 80; server_name www.maotai.com; location / { root html; index index.html index.htm; } } server { listen 80; server_name www.daolian.com; location / { root html/www; index index.html index.htm; } }} 访问测试
防盗链效果
- 拓扑图
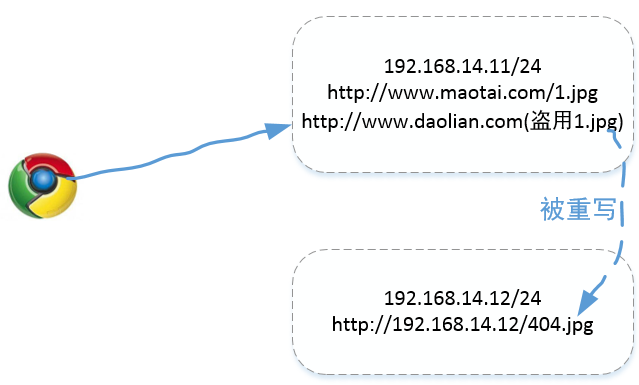
- 要实现的效果
(n1)www.maotai.com/qq.jpg(n1)www.daolian.com #实现效果: 盗用qq.jpg链接时, 将盗链的连接改为www.192.168.14.12/404.jpg(n2)www.192.168.14.12/404.jpg
- n1访问qq.jpg正常访问时候没问题
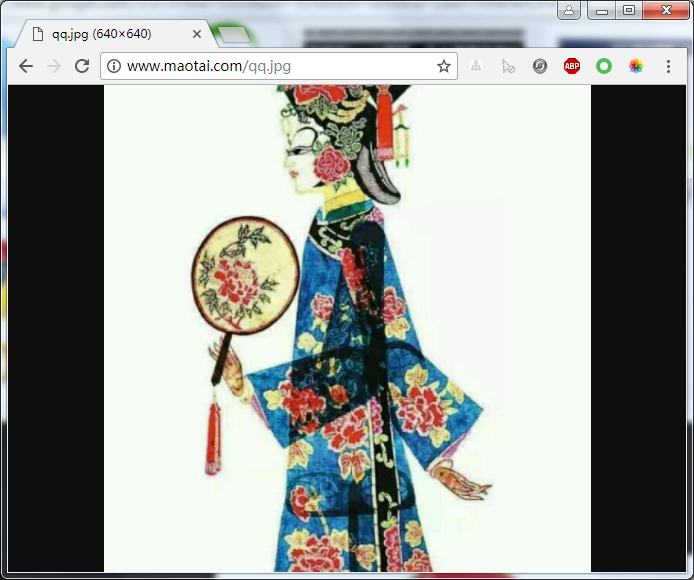
- 盗链服务器访问
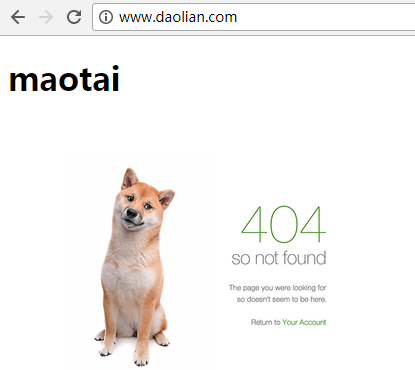
未盗链时应该是这样的

nginx.conf
worker_processes 1;events { worker_connections 1024;}http { include mime.types; default_type application/octet-stream; sendfile on; keepalive_timeout 65; server { listen 80; server_name www.maotai.com maotai.com; location / { root html; index index.html index.htm; } location ~* \.(gif|jpg|png|swf|flv)$ { valid_referers none blocked *.maotai.com; if ($invalid_referer) { rewrite ^/ http://192.168.14.12/404.jpg; #注这里要重新找台服务器, 如果同一台,我没做出效果 #return 404; } } } server { listen 80; server_name www.daolian.com; location / { root html/www; index index.html index.htm; } }} 